Considered the founding work of science fiction, Mary Shelley’s classic Frankenstein has served as explanation and warning across many subjects and issues since it first captured the imaginations of readers. The context within which she wrote, exactly two centuries ago as the Industrial Revolution was gaining speed, was the tumult of Humanity’s first failures against a rising tide. Today, as the casualties of the first years of this new Cyber Revolution fall and the sharp changes already emergent shake our reality, the moment is nigh to revisit Shelley’s warnings, to consider the ramifications of the past upon life and the planet, and to ponder the future.
Published in 1818, Frankenstein is the perfect foil to interrogate the cost of past choices as new ones arise. Shelley wrote the book when the perils of that great socio-economic change were already manifesting even as its promise beckoned. The Luddites of her day, the movement of the first workers displaced by industrial manufacture, were only the first of many casualties across the human and natural landscape. Today, however, as the complex costs and consequences of that advance in human experience are manifest, the work easily stands as a rebuke of Man’s unchecked rush to apply his knowledge and ability to change thereby creating a monster. Although Man rectified many of the Industrial Revolution’s early and simpler abuses of men and nature, its long term effect, and the looming complex climate and human crises it brought, threaten much of the existence we take for granted. Looking at the results of the Industrial Revolution writ large, we must examine the positive, beneficial effects for society against the negatives, most significantly in climate change, pollution, geographic-topographic degradation, and the unsettled terrain of human satisfaction with their daily lot.
Cyber-Industrialization
Looking back on the Frankenstein’s monster of unchecked industrialization, it is worth asking which of the advances might have been challenged in their own time had we known the true costs. Some? Many? None? Surely reason would have promoted a demand for moderation and acted as a brake upon the unchecked application of industrialization to the majority of humanity’s endeavors. At the very least, one might expect governing authorities to impose the costs of the advances upon those who would profit most from them. Such a hypothetical is no mere wistful navel gazing: to reflect on what to rework in the contested present is more than relevant as Mankind stands at the next great socio-economic revolution. As we face a similarly grand reconfiguration of humanity, changes being wrought under the Cyber Revolution offer a means to reconsider the choices for our future and reckon the errors of our past. We would do well to address these storms now rather than later. Looking only at a snapshot of issues arising from artificial intelligence, algorithms, the increasingly networked world, and their further implications on the quotidian purpose of life, the terms of our necessary humility emerge.
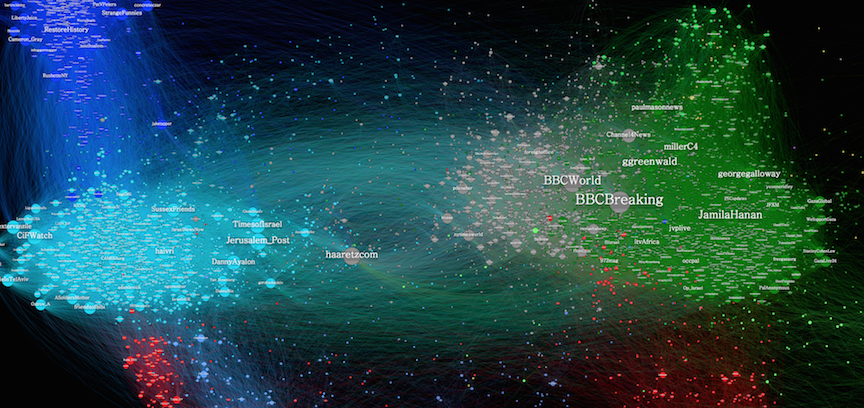
If sentience is mankind’s defining characteristic, then artificial intelligence and the role of algorithms are profound efforts to reproduce our very essence. Controlling significant swathes of life, these human creations hold to capacity usurp sovereignty over human existence. Already the machines taught to converse are learning to do so in self-created languages – it will not be long before they can do so to their human creators’ utter incomprehension. Perhaps worse than the science fiction horror of a world controlled by machines is the banal disaster of a world remade by distrust and unreality. The social media that more and more of the population rely upon are subjected to ever more sophisticated manipulation by algorithms. Created to shape content tailored to an individual’s tastes, the dark side of this phenomenon is algorithms designed to influence the fundamental core of representative governance. And while propaganda and false news are nothing new, the targeting and volume is creating an unprecedented environment of uncertainty about the very terms of reality.
Where humanity organized itself for good and ill in the creation of communities, this urge to connect as applied to the new cyber world cedes even more control to the unknown. The networked world increasingly places critical functions at finger-tap reach of individual and non-state actors whose motives and ends benefit few and harm many. Looking only at recent events, the systems and institutions under siege to the “Internet of Things” are those most critical to society; a window to the perils of this newest ungoverned space. The Equifax hack reported last month, affecting at least 143 million Americans, is only the latest largest data breach in history, and may threaten the financial security of too many. Ransomware attacks are increasingly used to take control of information systems, putting health at risk as hospitals have become targets to virtual hostage taking for money. But the worst may be the peril of the electronic means to our democratic system. The investigation into the possible hacking of the 2016 election illuminates a chillingly effective attempt to interfere with American sovereignty. While the extent of this campaign is as yet unknown, evidence of theft of voter information in Illinois by likely Russian actors has been verified and is under Congressional investigation.
Humanity’s Monster
At a deeper level, the Cyber Revolution attacks the fundamental meaning and experience of what it is to be human. Looking to the single issue of work, so many advances threaten to continue the degradation of this human value begun during the Industrial Revolution. It is an ominous trend. Not merely a Protestant ethic, there is something fundamentally important about work to human existence that links fulfilling a sense of productivity to meaning. Yet as the Cyber Revolution gathers momentum, robots and computers may perilously curtail productive human activity from agriculture to automotive, architecture to artisan cheese. The wisdom of prioritizing more goods at cheaper prices over simple human satisfaction demands a rethink as more radicalism arises from nihilism born of meaninglessness.
These are just the first rounds; this era’s first artisans displaced by factory machines, rivers despoiled, air befouled. Without succumbing to full-fledged Ludditism and the rejection of all advances, there is a need to rethink this headlong rush into the next era of change. The genius of our Frankenstein impulse, the creative imagination to dream and explore, should not be destroyed – but neither should the monsters of this impulse be allowed to rampage unfettered.
 Dr. Jill S. Russell is a Professor of National Security and Strategy at the U.S. Army War College. She has worked extensively in professional military education in the U.S. and the U.K., as well as in defense consulting. Her areas of expertise and research interest are logistics, urban conflict and public order, and strategy and policy. She writes and comments regularly on military affairs and national security for blogs, news outlets, and practitioner publications.
Dr. Jill S. Russell is a Professor of National Security and Strategy at the U.S. Army War College. She has worked extensively in professional military education in the U.S. and the U.K., as well as in defense consulting. Her areas of expertise and research interest are logistics, urban conflict and public order, and strategy and policy. She writes and comments regularly on military affairs and national security for blogs, news outlets, and practitioner publications.