If you are reading this article you are probably a user of social media. If you have been using it for a while, you may even realize the power of social media to inform, shape perceptions, create communities, and of course, to misinform. There is no doubt we can learn a tremendous amount of things from reading Twitter for example but we often overlook the potential of social media to provide understanding. There is a myth in military circles, a social media myth, that if we look hard enough, we will find some golden tidbit that will tell us how to win. No one makes this mistake more often or more decisively than senior military officers seeking accurate intelligence to drive operations. While most avoid social media themselves, they know it makes available a tremendous amount of information, and to a greater or lesser degree they all give lip service to its importance. But the disappointing fact is that the vast majority of senior military officers have no idea whatsoever how to maximize social media to benefit their intelligence and operations processes. Worse, these officers are learning exactly the wrong lessons about social media from faulty training simulations entrenched in military exercise programs.
The Social Media Problem
Why do I pick on senior military officers? Because although they accept social media is important, they almost uniformly resist using it. Their reasons range from concerns about privacy and security, to perceptions that social media is a venue for teenage nonsense rather than the serious business of military commanders. This lack of engagement and experience with the tool deprives them of understanding and leads to misperceptions. A perfect example of this is a recent story about a successful air strike in Syria against a command post of the Islamic State of Iraq and the Levant (ISIL). According to a statement from the commander of US Air Combat Command (ACC), their targeting staff derived the location of the headquarters from an ill-advised post by a Twitter-happy ISIL fighter. While this sounds like a terrific victory, combing through tweets for actionable intelligence is probably a waste of time and misses the real value of social media sites that are more useful as a source of big data than of targeting data.
Take Twitter as an example. Twitter averages about 500 million “tweets” per day. Just to put that into perspective, that’s 6000 tweets per second. Even with automated tools, finding one tweet that contains useful information is an enormous effort to say the least and it’s only the beginning. Interpreting the accuracy and reliability of a single tweet will be very difficult indeed. Here’s why: a tweet is 140 characters of data with extra allowances for hyperlinks, pictures, and location data. There’s not a lot to go on there and while a tweet is attributable to the person that generated it, that person’s identity can never really be verified. Let’s ponder for a moment the fact that according to ACC, a military officer somewhere made a decision to drop ordnance based on the digital equivalent of an address scribbled on a piece of paper by an unknown individual and posted on a bulletin board with millions, no, billions of other similar notes. That’s an incredibly low standard by which to make such decisions and the possibility is extremely high that there is more to the story than is available in the tweet. Though we have to assume there were other sources of intelligence applied to verify this target, this is not what ACC’s statement suggested and it does not change the fact that they must have spent an enormous amount of man hours and computing power to find and interpret that tweet. The question is: was it worth it? ISIL will undoubtedly tighten up its operational security, making this kind of targeting even more rare than it already is. Worse, ISIL will learn from this. What’s to stop them from falsifying targets, wasting coalition resources or luring it to drop bombs that will cause civilian casualties or worse? When that happens, and it will happen, the use of single-source data from unverifiable individuals will come into serious question as a basis for targeting decisions.
Reinforcing Bad Habits
Surely the intelligent and well-trained staff officers of the United States Military have figured this out. But they have not figured it out, or at least the most senior leaders among them haven’t. Senior military officers that range in age from the late-30s to the mid-60s simply did not grow up with social media as a part of their lives. Some have started to use it but are bucking a military culture that is social media-skeptical. Secondly, although American officers are generally well-trained, they are trained in the wrong techniques when it comes to social media. To illustrate, consider one aspect of the synthetic social media environment used in exercises at NATO’s Joint Warfare Center (JWC).
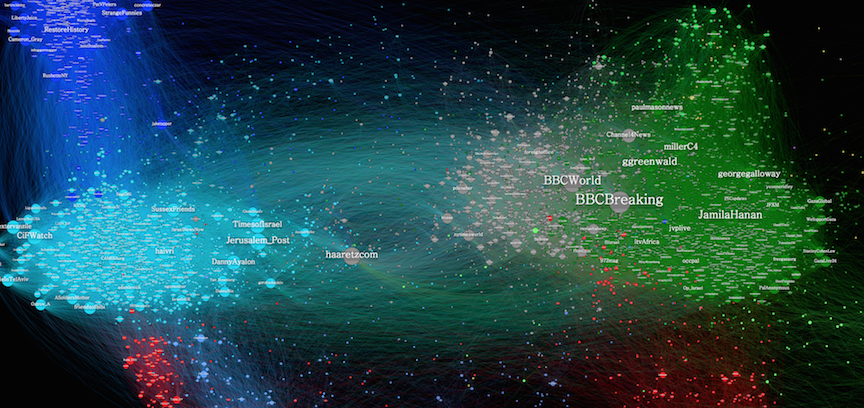
JWC replicates Twitter with a system called “Chatter”. Chatter is very similar to Twitter in that a “chatt” is a short text message that allows attachment of photos and similar files. Hyperlinks are not used because Chatter is only available on NATO classified computer networks to prevent leakage of exercise information into the real world. This is not a trivial point. Leakage of scenario graphics from a US military exercise in 2015 caused an uproar in Texas when citizens discovered the Pentagon had labelled their state “hostile” for exercise Jade Helm. Keeping Chatter on classified networks limits its scope to a ridiculously small sample; on average, the volume of chatts in an exercise might reach 300 a week. While the vast majority of that volume is useless “white noise”, some chatts inject useful information into the exercise to cause a specific response by the training audience. Needless to say, in an information environment that tops out at 300 inputs a week, intelligence staffs stand a good, yet thoroughly unrealistic chance of finding the needle in the very small haystack. This sends two very strong and misleading messages about social media to Allied commanders. One is that they can and should expect to find useful bits of actionable intelligence hidden amongst social media posts. Secondly, even if commanders are thinking about analyzing trends and relationships between communities, Chatter is completely incapable of providing the volume of data required to do so. The system simply discourages commanders from understanding what is arguably the most valuable characteristic of social media, which is that big data can reveal broad truths about an environment. [For an example of how this can support understanding and decision making, see this fascinating Wired Magazine article.]
Big Data, Not Targeting Data
Continuing to perpetuate the social media myth will further entrench the wrong lessons in the minds of our commanders and ensure that using social media for targeting is the enemy of using it for understanding. Making social media sites like Twitter a useful or reliable source of information will require too much in the way of resources and will produce too few positive results and indeed increasingly negative ones as the enemy adapts. Western militaries simply must change their approach to social media as a tool, viewing it not as a source of targeting data but as a gateway to big data. Training aides like Chatter must replicate big data but doing so will require involvement of the public. While this is not easy and carries significant risk, it is manageable risk.
Lino Miani is a retired US Army Special Forces officer, author of The Sulu Arms Market, and CEO of Navisio Global LLC.


Here’s an interesting real world use of Twitter for awareness. http://www.scotsman.com/news/politics/top-stories/north-sea-protected-by-fishing-boats-and-twitter-1-3837240